SCIM: Automate user provisioning with Okta
This topic provides the instructions that you need to follow in KACE Cloud and Okta to automatically provision and de-provision users and groups to KACE Cloud.
The System for Cross-domain Identity Management (SCIM) specification is used to perform provisioning actions between Okta and KACE Cloud.
The scenario outlined in this tutorial needs the following prerequisites:
- An Okta directory and user credentials with Admin access to your Okta portal
- A KACE Cloud tenant
- A user account in a KACE Cloud tenant with a System Admin role.
For more details about Okta SCIM configuration, see Okta: Provision applications.
|
|
TIP: Assign a single Okta user to KACE Cloud to test the automatic user provisioning configuration. You can assign additional users and groups later, as required. |
To automate user provisioning with Okta:
- Set up KACE Cloud for user provisioning.
- Sign in to KACE Cloud.
- SSO users imported through LDAP Sync only. Disable the default password for users.
- On the Settings tab, navigate to KACE Cloud > Settings.
- On the KACE Cloud Settings page, in the Users section, ensure the Use a default user password for users imported via LDAP Sync check box is cleared.
- On the KACE Cloud Settings page, click Save.
For more information about this page, see Explore KACE Cloud Settings.
- Enable user provisioning using SCIM in KACE Cloud.
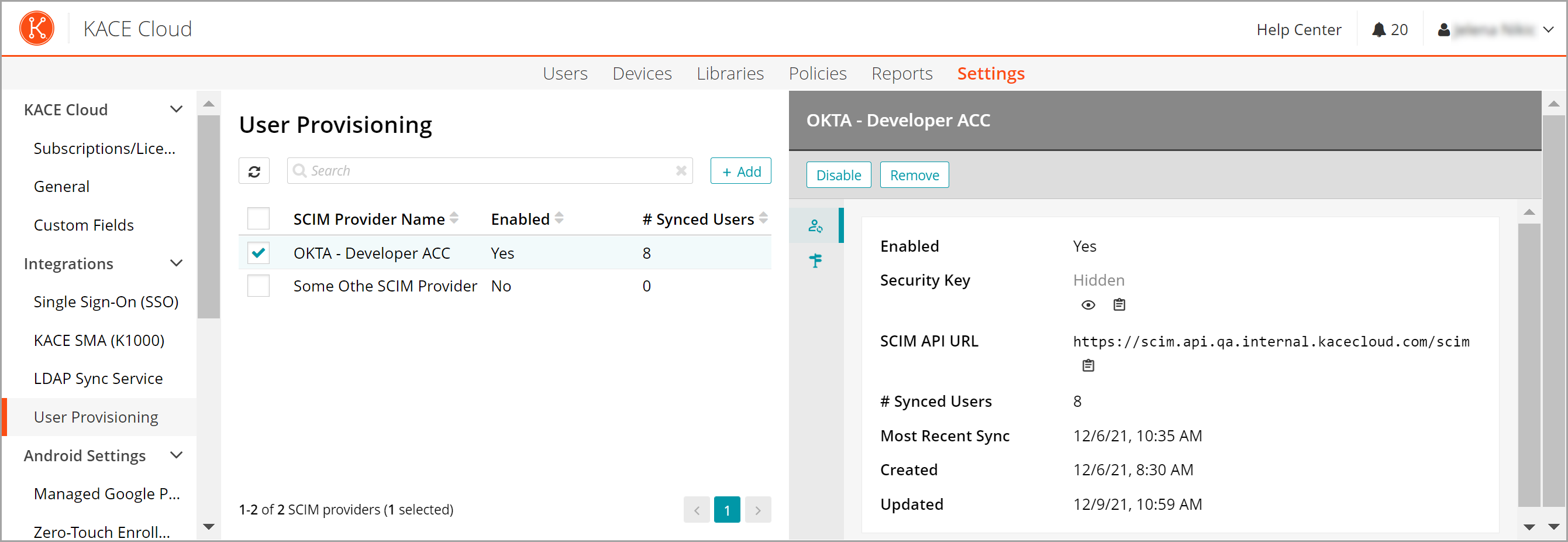
- In to KACE Cloud, on the Settings tab, navigate to Integrations > SCIM User Provisioning.
- Create a new SCIM provider for your Okta tenant.
- On the User Provisioning page, click Add.
- Type a provider name. For example: Okta.
- Select the Enabled check box to enable SCIM user provisioning from Okta.

TIP: You must do that now so that a security key required by Okta is generated.
- Click Save.
- Copy the contents of the SCIM Service URL and Security Key fields for later use.
This information is required for the Okta application integration.
- In to KACE Cloud, on the Settings tab, navigate to Integrations > SCIM User Provisioning.
- Configure user attribute-mappings in KACE Cloud.
- After creating the new SCIM provider, use the Mappings tab of the newly created SCIM provider to manage the user attribute-mappings between various SCIM user schema attributes and the KACE Cloud user fields. When creating a new mapping, you can do any of the following:
- Select a SCIM user schema attribute from the supported builtin SCIM 2.0 enterprise user schema attribute.
- Define a custom SCIM user extension attribute, and the select a built-in KACE Cloud user attribute.
- Define a KACE Cloud custom user field to map it to.
- If there are other user attribute values you want to map from SCIM for their KACE Cloud users, you can first define the custom KACE Cloud user fields on the Settings > Custom Fields page in the Users tab, and then return to this attribute mappings page to map the desired SCIM attribute to them.
Here are some commonly suggested mappings that require you to first create the specified custom KACE Cloud user field on the the Custom Fields page, in the Users tab.
SCIM attribute
KACE Cloud user field
KACE Cloud field type
Notes
urn:ietf:params:scim:schemas:extension:enterprise:2.0:User:manager.value
Manager
custom
urn:ietf:params:scim:schemas:extension:enterprise:2.0:User:department
Department
custom
urn:ietf:params:scim:schemas:extension:enterprise:2.0:User:organization
Organization
custom
phoneNumbers[type eq \"mobile\"].value
Mobile
custom
urn:ietf:params:scim:schemas:extension:enterprise:2.0:Group:externalId
Groups
custom
This populates the named custom KACE Cloud user attribute with a comma delimited of groups Okta reports that the user belongs to. This is dependent upon user Group provisioning being enabled in Okta.
- When you finish configuring user attribute-mappings between SCIM user schema attributes and KACE Cloud user attributes, save your changes.
To add or edit a mapping, on the Mappings tab, click Edit Mappings, and make your changes, as required.
When you configure a new SCIM provider, several required attribute-mappings are automatically set up. These mappings are required and cannot be modified or removed. You can create additional mappings from both supported built-in and custom SCIM user schema attributes to built-in and custom KACE Cloud user fields. The pre-populated required system managed read-only mappings are as follows:
SCIM attribute KACE Cloud user field KACE Cloud field type Notes userName Email builtin displayName Name built-in The SCIM attribute named displayName must be mapped to the KACE Cloud user field named Name. id HeliumKeycloakObjectGuid built-in The HeliumKeycloakObjectGuid is an internally used identifier that is not displayed on the user details page. active Disabled The value of the active SCIM attribute is reversed when it is mapped into the built-in KACE Cloud user field named Disabled. For example, if the SCIM active attribute has a value of true, the Disabled built-in KACE Cloud user attribute has a value of false. Other built-in KACE Cloud user fields that are commonly mapped to from SCIM attributes are Address, City, State, Zip and Country. Here are the suggested mappings for those fields and several other commonly used user attributes:
SCIM attribute
KACE Cloud user field
KACE Cloud field type
addresses[type eq \"work\"].streetAddress
Address
built-in
addresses[type eq \"work\"].locality
City
built-in
addresses[type eq \"work\"].region
State
built-in
addresses[type eq \"work\"].postalCode
Zip
built-in
addresses[type eq \"work\"].country
Country
built-in
- After creating the new SCIM provider, use the Mappings tab of the newly created SCIM provider to manage the user attribute-mappings between various SCIM user schema attributes and the KACE Cloud user fields. When creating a new mapping, you can do any of the following:
- Set up Okta application for KACE Cloud user provisioning.
- Sign in to the OKTA admin portal.
- In side navigation, select Applications > Applications.
- Click Browse App Catalog.
- In the search box, type SCIM 2.0 Test App (OAuth Bearer Token)and then select it in the displayed list.
- On the following page, click Add.
- In the General Settings - Required section, provide the following information:
Application Label KACE Cloud SCIM User Provisioning Application Visibility Ensure both check boxes are cleared. - Click Next.
- On the Sign-On Options - Required tab, please provide the following information:
Sign on methods Ensure SAML 2.0 is selected Credentials Details - Application username format Select Email from the list. Do not leave the default value. Credentials Details - Update application username on Ensure that Create and update is selected. - Click Done to finish the wizard and return to the new application settings pages.
- In the new KACE Cloud SCIM User Provisioning application, on the Provisioning tab, click Configure API Integration.
- Select the Enable API Integration check box.
- In the SCIM 2.0 Base URL field, type the SCIM API URL that you recorded in step 1. For example: https://scim.api.kacecloud.com/scim.
- In the OAuth Bearer Token field, type the Security Key that you recorded in step 1.
- Click Test API Credentials to have Okta attempt to connect to the SCIM endpoint. If the attempt fails, error information is displayed.
- Click Save to return to the Provisioning tab of the new KACE Cloud SCIM User Provisioning application.
- On the Provisioning tab of the new KACE Cloud SCIM User Provisioning application, under Settings, click To App.
- Click Edit next to Provisioning to App.
- Select the check boxes next to each of the following options to enable them:
- Create Users
- Update User Attributes
- Deactivate Users
- Ensure the check box next to Sync Password is cleared, this option is not supported when selected.
- Click Save.
- Back on the Provisioning tab of the new KACE Cloud SCIM User Provisioning application, scroll down to the KACE Cloud SCIM User Provisioning Attribute Mappings section of the page and click Go to Profile Editor.
- On the Profile Editor page, in the Attributes section, click Mappings.
- In the KACE Cloud SCIM User Provisioning User Profile Mappings, at the top of the page, click Okta User to Kace Cloud to display the SCIM attribute mappings.
- Set the following attribute mappings.
- Required attribute-mappings: Ensure that the following user mappings are configured as specified. Some might be there by default, others need to be either added or modified to match the details below.
Okta - Okta User User profile user SCIM - KACE Cloud SCIM User Provisioning User Profile appuser Notes user.displayName displayName This should be the user's full name (first and last names). If the Okta displayName field does not contain the user's full name, you can map the user.firstName + " " + user.lastName Okta field expression to the SCIM displayName field. - Suggested optional mappings: Specify these mappings using existing built-in Okta and SCIM user attributes:
Okta - Okta User User profile user SCIM - KACE Cloud SCIM User Provisioning User Profile appuser user.streetAddress streetAddress user.city locality user.state region user.zipCode postalCode user.countryCode country user.managerId managerValue user.department department mobile phoneNumbers[type eq \"mobile\"].value user.employeeNumber employeeNumber
- Required attribute-mappings: Ensure that the following user mappings are configured as specified. Some might be there by default, others need to be either added or modified to match the details below.
- When you finish configuring the field mappings, click Save Mappings.
- In side navigation, select Applications > Applications and then select KACE Cloud SCIM User Provisioning from the list.
- On the Assignments tab, click Assign button to select the Okta users and groups that you want to provision into KACE Cloud.
- On the Push Groups tab, click Push Groups button, then select either Find groups by name or Find groups by rule to select the groups' memberships that you want to send to KACE Cloud.
- For each desired group, in the Push Status - Active menu, click Push Now to trigger group membership with KACE Cloud.
- Monitor the the user provisioning service status of the Okta KACE Cloud SCIM User Provisioning application setup for KACE Cloud.
When you have configured provisioning inside of Okta, view the Okta provisioning logs:
- In side navigation, select Applications > Applications and then select KACE Cloud SCIM User Provisioning from the list.
- Click the View Logs link near top of the application settings.
- Monitor the status of the KACE Cloud SCIM user provisioning service.
In KACE Cloud, navigate to Settings > Integrations > SCIM User Provisioning and select the configured SCIM provider.
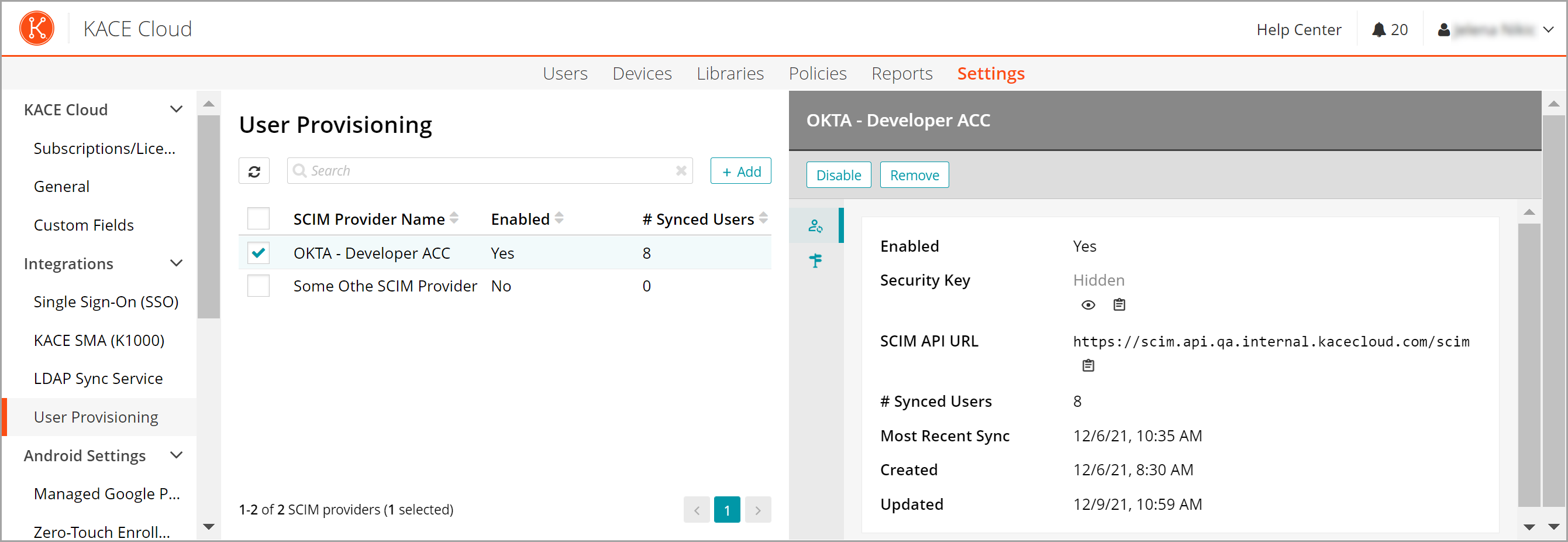
The details pane displays the following information:
- Provider Name: The name assigned to this SCIM provider when it was created.
- Enabled: Indicates if the SCIM user provisioning service is enabled for this provider. When disabled, KACE Cloud ignores any SCIM processing requests from the SCIM provider.

NOTE: If this setting is disabled, and then re-enabled, a new Security Key is generated, and you must update the corresponding Okta KACE Cloud SCIM User Provisioning application > Provisioning > Integration > OAuth Bearer Token field with this new security key value.
- Security Key: The security key value needed by the corresponding Okta application integration.

NOTE: This value should be kept secret. If this value it is ever compromised, a new secret key can be generated, invalidating the old security key value. See the above note about the Enabled setting.
- SCIM API URL: The value needed for the Tenant URL field when setting up provisioning on the Okta KACE Cloud SCIM User Provisioning application.
- # Synced Users: The number of users which are synchronized by the SCIM provider.
- Most Recent Sync: The date and time of the last successful synchronization activity from by SCIM provider.